Achieving online privacy and security is not an easy feat, so that’s why we created this email security and privacy course to enrich the learning and awareness of our users. For that reason, we made a content-based course by putting together all the important and related aspects of email security and privacy.
The entire course takes around an hour of your reading. We have presented it in a number of short blog posts categorized into three parts. The course itself is easy to understand and you don’t need to be a privacy or security expert to make it work for you. We hope our course will help you in raising the bar of your email data security and privacy!
Set your personal threat profile
We do realize that many people can feel overwhelmed by the number of tips and recommendations put forth. This may make you feel like there’s little hope out there, and that many of the tips are for security experts.
Essentially, it is about finding a good balance between security and convenience. So, you just need to determine yours.
- Assess the risk you are comfortable with
This will allow you to identify what security measures are relevant to you. For example: do you feel you need to send all your text messages with end-to-end encryption via a specific app?
- Security precautions can range from easy one-time changes to long-term shifts in habits
Security takes work. Doing nothing is so much easier than doing the work needed to make yourself more secure.
- Just because you are not at ease with technology does not mean you can ignore security
A good judgement is always needed, but it is worth doing a little internet surfing if there is a term you are not familiar with before ruling something out.
After setting your personal threat profile, you will be in a position to see which advice/tip suits you best.
This email security and privacy course addresses most of the common threat models of end users.
Email privacy and security awareness course: Part 1
- Protect your data – 4 min read
Protecting your data is the very first step in securing your digital life, therefore do not hesitate to take action.
- Protect your device – 3 min read
Protecting your device is the second and most important step. Therefore, you need to understand that your device is the gateway to your digital life. The more secure it is, the more effective your defense measures will be.
- Keep your email account secure – 2 min read
Securing your email account means protecting your online identity since your email address is associated with almost everything you do online.
- Bad Password Habits – 3 min read
Following good password habits is a key factor in making all of your online and offline defenses stronger. There certainly are password managers, that do a great job. However, avoiding bad password habits is something that you should do yourself.
- 11 Password Best Practices – 7 min read
Once you drop bad password habits you’ve been making, here are 11 best practices to adopt to ensure your passwords are strong.
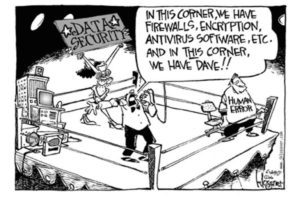
- Social Engineering
Humans are considered as the weakest link in any sort of defense. The thing that make us vulnerable is the tendency to trust someone or something based on certain criteria. This section will briefly go through different kinds of social engineering.
– What is Social Engineering? – 6 min read
Social engineering are a group of techniques that cybercriminals use that exploit the human nature and trick people to do something that will weaken their security.
– Social Engineering: What is Tailgating? – 2 min read
Tailgating (piggybacking) is a social engineering technique in which one tries to enter an area they are normally not allowed to go in, usually be following someone closely behind.
– Social engineering: Quid Pro Quo attacks – 2 min read
Sometimes bad actors can trick you into thinking they are doing you a favor that you need to return. But, no matter if you willingly give them your sensitive data or not, they can always use it to steal money and more data.
– Social Engineering: What is baiting? – 2 min read
People like winning prizes. Doesn’t matter if they actually signed up for the game or not. Except that your privacy and security is worth much more than that.
– Social Engineering: What is pretexting? – 3 min read
The best lies revolve around a good pretext and hackers know this well enough. That’s why they’ll try to use all kinds of fabricated scenarios to trick you into giving them your data.
– Social Engineering: What is Phishing? – 5 min read
In the Q3 2022 there were 1,270,883 phishing attacks. Phishing is getting more and more sophisticated and is the number one threat that email users need to keep an eye on.
– Social Engineering: What is Spear Phishing? – 11 min read
If phishing is like casting a wide net and hoping to catch a few small fish, spear phishing is using a harpoon to catch the big fish.
– Social Engineering: What is Vishing? – 5 min read
Not every type of phishing uses email. In vishing, for instance, the scammer uses the phone to trick people into giving their personal information. Unfortunately, this scam is most effective with elderly folk, so if you have someone like that at home help them understand that the “nice man” on the other end is only after their money.
– Social Engineering: What is Smishing? – 3 min read
Did you know that 95% of texts are read in just 3 minutes after sending? And the average respond is 90 seconds! People often don’t even read or check the message before responding.
– Social Engineering: What is Scareware?– 7 min read
You have a virus! Or is it just what the scammers would have you believe?
– Social Engineering: What is Shoulder Surfing?– 5 min read
Sometimes, you need to have eyes on the back of your head. Because you can never know who is looking over your shoulder and stealing your information.
– Social Engineering: What is Whaling? – 8 min read
Why catch small fish when you can get a lot more from the big kahuna is the logic behind this social engineering attack that targets the companies leaders and bosses.
– Tips on how to avoid social engineering schemes – 3 min read
Here are 11 tips to avoid social engineering attacks.
Email privacy and security awareness course: Part 2
- Prevent your device on becoming a zombie? – 3 min read
Lets now discuss some of the consequences that could occur in case your device or account gets affected with a malware. We’ll also go through the steps that you can take to avoid such a situation.
- Protect yourself from ransomware – 3 min read
Another potential consequence of a compromised device or account is ransomware. This post will discuss the related aspects in detail.
- Email privacy expectations! – 4 min read
The myriad ways we send, receive, store, and use email messages make securing and enhancing email privacy a very difficult problem. This blog post gives you an overview of resulting privacy issues.
- Safeguard your online privacy – 2 min read
Are you in control of your online data? This blogpost gives some steps you can take to improve privacy of your online data.
- What is Email Spoofing and How to Spot it? – 4 min read
Email addresses can be forged to look legit. This blogpost gives you tips to spot email spoofing and solutions against it.
Email privacy and security awareness course: Part 3
- Protect your data when crossing borders – 4 min read
It is important to understand your rights in order to protect your data when crossing borders. This post will discuss the related aspects and some of the protection measures that you can take.
- Protect your devices when traveling – 4 min read
This blogpost expands further on protecting devices while traveling in particular.
- Virtual machine: why use it? – 3 min read
Do you like isolating your digital workspace? This blogpost give reasons to use a virtual machine or VM from security and privacy stand-point.
- Biggest email security mistakes – 6 min read
We all make mistakes. Here are 7 email security mistakes most people are guilty of that you need to avoid.
- Steps to take when your Email is hacked! – 4 min read
Oh no, your email has been hacked! Let’s see what you can do about it.
Useful resources
Taking measures and following good practices are great but they don’t guarantee that your account will never be compromised. This blogpost provides some immediate steps you can take to regain access to your account and prevent future hacking attempts.
At Mailfence, not only do we aim to make our platform more private and secure, we also try to make our users aware of the importance of improving their email security and privacy in general. Following are some of the direct links of Mailfence specific blog posts:
- Mailfence threat model
- High-level security analysis
- Why mailfence is a unique secure and private email service
- Mailfence transparency report and warrant canary
- Mailfence and user data security, privacy and anonymity
- Harden your Mailfence account
- Send email anonymously using Mailfence and Tor
- Using a VPN & Mailfence
We believe that a secure and private digital world can only be achieved if both the creators and users play their respective parts. We hope that this course will prove useful, while we continue to strive in making your emails more secure and private.
However if you still have some friends/colleagues who would ask why to take such a course, then following comic will suffice.
Should you have any more questions, please don’t hesitate to let us know.