Phishing ist eine Variante von Social-Engineering-Angriffen, bei der sich Cyberkriminelle als vertrauenswürdige Quellen ausgeben, um ihre Opfer zur Preisgabe persönlicher Daten oder zum Herunterladen von Malware zu verleiten.
Nach Angaben des National Institute of Standards and Technology (NIST) gibt es jedes Jahr immer mehr Phishing-Angriffe, mit einem überwältigenden Anstieg von 61 Prozent seit 2021.
Diese Statistiken zeigen die Verbreitung von Phishing-Angriffen im Jahr 2023 und die Notwendigkeit, sich dagegen zu schützen. Erfahren Sie in diesem Artikel, wie Phishing funktioniert, wie Sie ihm aus dem Weg gehen und wie Sie sich und Ihr Unternehmen schützen können.
Mailfence - Erhalten Sie Ihre kostenlose, sichere E-Mail.

4.1 basierend auf 177 Benutzerbewertungen
Mailfence - Erhalten Sie Ihre kostenlose, sichere E-Mail.

4.1 basierend auf 177 Benutzerbewertungen
Was ist Phishing?
Phishing (ausgesprochen „fisching“) ist eine Form des Identitätsdiebstahls. Bei dieser Art von Social-Engineering-Angriffen werden Privatpersonen oder Unternehmen getäuscht, mit dem Ziel, sensible Informationen zu stehlen oder Malware zu verbreiten. Diese Angriffe erfolgen häufig per E-Mail, in denen die Cyberkriminellen vorgeben, eine vertrauenswürdige Quelle zu sein.
Gängige Phishing-Taktiken zur Täuschung
Bei solchen Täuschungen kann es sich um diese Beispiele handeln:
- Imitieren einer Person oder einer Organisation, die Sie kennen, wie zum Beispiel Ihre Bank oder eine*r Ihrer Kolleg*innen.
- Gefälschte URLs, die legitime Websites nachahmen, denen Sie vertrauen, mit dem Ziel, Zugangsdaten zu erfassen. Diese gefälschte Website wird zu dem Zweck eingerichtet worden sein, an die Zugangsdaten von Nutzer*innen zu kommen.
- Einige scheinbar nützliche Dateien, zu deren Download Sie aufgefordert werden, enthalten einen Trojaner, in dem sich Schadsoftware (Malware) verbirgt.
In letzterem Fall kann es sich bei der versteckten Schadsoftware um Folgendes handeln:
- Spyware (Spionageprogramme), die Daten sammeln und Sie ausspionieren soll.
- Malware, die darauf abzielt, eine Schwachstelle zu schaffen, zum Beispiel, indem Sie eine Hintertür in Ihrem IT-System einbaut oder Ihr Gerät in ein Zombie-Gerät verwandelt.
- Ransomware, eine heutzutage immer häufiger eingesetzte schädliche Software, die das Gerät des Opfers zum Einfrieren bringt. Um es zu entsperren, müssen Sie ein Lösegeld zahlen.
Wie sehen Phishing-Angriffe aus?
Es gibt verschiedene Arten von Phishing-Angriffen, die davon abhängen, welche Taktik der*die Hacker*in anwendet, um mit seinem Opfer in Kontakt zu treten:
- Klassisches Phishing: Die „Fischer“ senden massenhaft E-Mails an beliebige Personen. Diese Nachrichten sind alle identisch und enthalten einen Link auf eine gefälschte Website, um den*die Leser*in dazu zu bringen, dort seine*ihre Zugangsdaten einzugeben. Oder sie fordern den*die Adressat*in auf, eine angehängte Datei herunterzuladen, die mit Malware infiziert ist.
- Spear Phishing: Eine Phishing-Attacke, die auf Organisationen und bestimmte Personen abzielt, anstatt Massen-E-Mails zu versenden.
- Smishing: Ein Phishing-Angriff, bei dem anstelle von E-Mails SMS versendet werden. Die Bezeichnung stammt aus der Kombination der Wörter SMS und Phishing.
- Vishing: Bei dieser Phishing-Attacke versucht der*die Täter*in, Sie mittels seiner*ihrer Stimme während eines Telefonanrufs dazu zu bringen, eine Aktion auszuführen.
- Whaling: Ein Angriff, der auf „große Fische“ abzielt, also zum Beispiel auf leitende und geschäftsführende Mitglieder einer Organisation. Sie werden in der Regel dazu gebracht, eine Aktion wie die Überweisung eines großen Geldbetrags auszuführen, was dem*der Angreifenden enorme Gewinne einbringt.
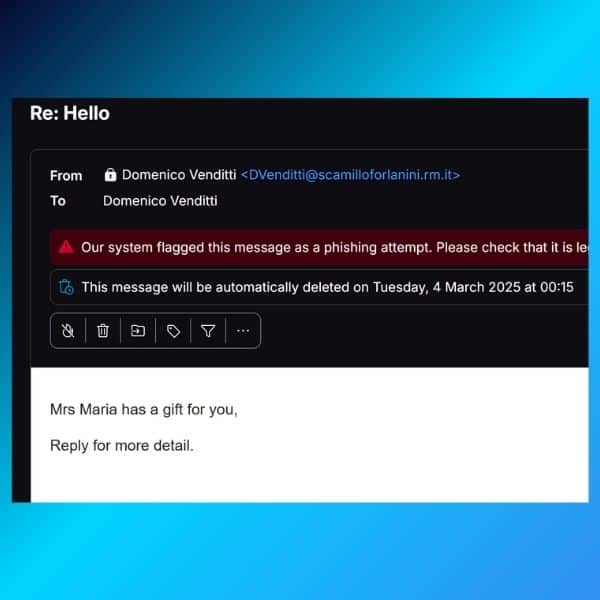
Nachfolgend finden Sie zwei Beispiele für Phishing-E-Mails:
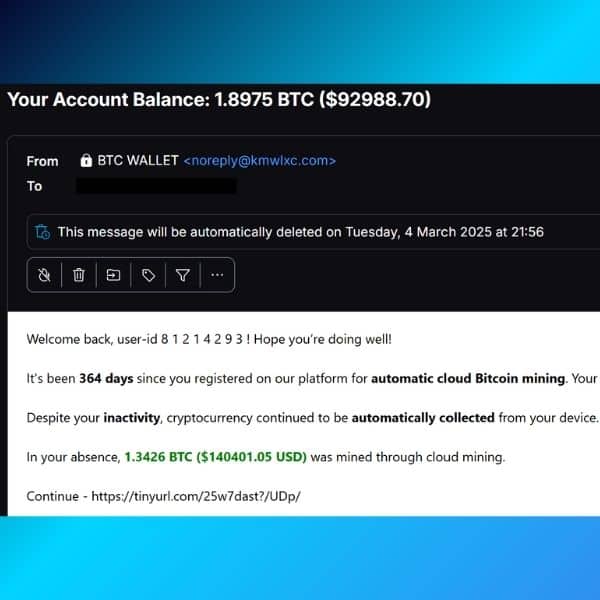
Im ersten Beispiel hoffen die Angreifenden, dass Sie auf den gesendeten Link klicken. Das eigentliche Ziel des Links ist dank des Kurz-URL-Diensts (URL Shortener) verborgen.
Im zweiten Beispiel hoffen sie, mit Ihnen in einen Dialog treten zu können. Pro-Tipp: In der zweiten E-Mail steht dieselbe E-Mail-Adresse im Absender- und Empfänger-Feld (Von und An). Das bedeutet, dass die tatsächlichen Empfänger*innen der E-Mail (wie Sie selbst) alle in Bcc stehen – und das wiederum heißt, dass diese E-Mail wahrscheinlich an Hunderte Personen gleichzeitig gesendet wurde.
Phishing-Versuche bei Mailfence
Auch unsere Nutzer*innen bei Mailfence werden manchmal Opfer von Phishing-Versuchen. Die Angreifenden geben in der Regel mittels E-Mail-Spoofing vor, dass sie eine Benachrichtigungs-E-Mail im Namen von Mailfence versenden. Hier ist ein Beispiel:
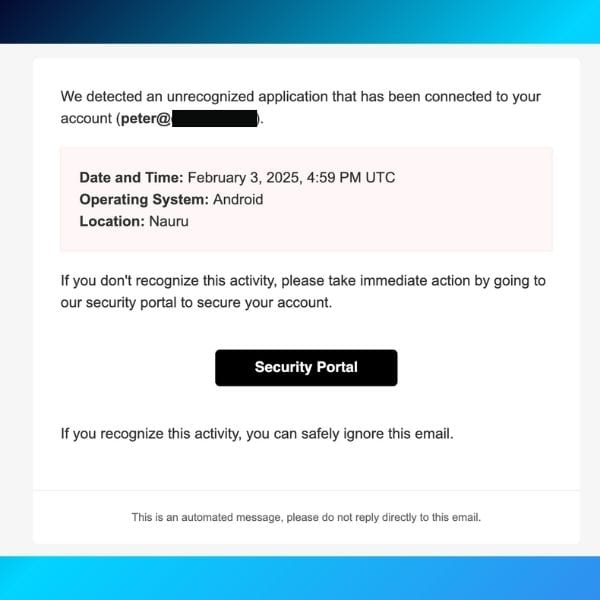
Bei diesem Phishing-Versuch erstellen die Angreifenden eine gefälschte Benachrichtigung. Das Ziel ist es, Sie glauben zu lassen, dass jemand auf Ihr Konto zugegriffen hat. Wenn Sie auf den Link klicken, könnten Sie unwissentlich Malware herunterladen, ohne es zu wissen. Oder Sie könnten auf eine gefälschte Mailfence-Website umgeleitet werden, die versucht, Ihre Zugangsdaten zu stehlen.
Was ist in diesem Fall zu tun?
Folgen Sie diesen Schritten. Dabei gilt der erste Grundsatz: Klicken Sie niemals auf einen Link und öffnen Sie niemals einen Anhang, bevor Sie die folgenden Prüfungen durchgeführt haben:
- Überprüfen Sie die E-Mail-Adresse des*der Absender*in. Vergewissern Sie sich, dass der Domainname tatsächlich @mailfence.com lautet (im obigen Fall ist das nicht so).
- Bewegen Sie den Mauszeiger über den Link, um die vollständige URL zu sehen. Klicken Sie ihn nicht an, wenn es sich nicht um eine Mailfence-Domain handelt.
Wie erkennen Sie eine Phishing-Nachricht?
Neben der Installation eines Anti-Spam-Filters und einer Sicherheitssoftware ist die beste Methode zur Bekämpfung von Phishing-Betrugsmaschen, diese als solche zu erkennen.
Früher waren Rechtschreib- und Grammatikfehler in einer E-Mail ein gutes Anzeichen für einen Phishing-Angriff. Aber heutzutage werden Phishing-Angriffe immer raffinierter, und Phishing-E-Mails sind oft perfekt geschrieben.
Sie müssen sich also auf andere Details konzentrieren, die einen Täuschungsversuch offenbaren:
- Links in der E-Mail. Machen Sie es sich zur Gewohnheit, mit dem Mauszeiger über alle Hyperlinks in einer E-Mail oder SMS zu fahren, um zu überprüfen, ob sie mit der Seite übereinstimmen, zu der sie Sie laut der Nachricht führen sollen. Bei nicht übereinstimmenden URLs (oder irreführenden Domainnamen) kann es auch passieren, dass sie zu .exe-Dateien führen, in die Malware eingebettet ist.
- Links in einer E-Mail, die Sie zum Besuch einer Website einlädt. Seien Sie zum Beispiel besonders vorsichtig bei „Ausverkaufs“- oder „Outlet“-Websites, die scheinbar mit einem legitimen, renommierten Einzelhandelsportal verlinkt sind. Es könnte sich dabei um eine täuschend echt aussehende Website handeln, die nur erstellt wurde, um Ihre Identität oder Ihr Geld zu stehlen.
- Drohungen. Haben Sie schon einmal eine Drohung erhalten, dass Ihr Konto geschlossen wird, wenn Sie nicht auf eine E-Mail reagieren? Cyberkriminelle setzen häufig Drohungen ein. Sie schicken Ihnen eine gefälschte Warnung, laut der angeblich Ihre Sicherheit gefährdet ist, aufgrund Ihrer Untätigkeit ein Dienst eingestellt wird oder Ihr Bankkonto überzogen ist.
- Nachrichten, die vortäuschen, von beliebten Websites oder Unternehmen zu stammen (Spoofing). Falls Sie eine Nachricht von einer vertrauenswürdigen Organisation, einem*einer Kolleg*in oder einem*einer Freund*in erhalten, in der Sie zu einer bestimmten Handlung aufgefordert werden, achten Sie auf diese Warnzeichen:
- Anfragen nach persönlichen Informationen jeglicher Art
- ein Angebot, das zu gut ist, um wahr zu sein, oder Geld, das Sie erhalten oder senden sollen
- alle Aktionen, die Sie nicht selbst initiiert haben
Alles, was irgendwie nicht richtig aussieht, sollte Ihr Misstrauen wecken. Selbst E-Mails, die scheinbar von bestimmten Organisationsarten wie Wohltätigkeitsorganisationen oder Regierungsbehörden stammen, können gefährlich sein. Angreifende nutzen oft aktuelle Ereignisse und bestimmte Zeiten des Jahres aus, beispielsweise:
- Naturkatastrophen (wie Erdbeben oder Wirbelstürme)
- Schrecken im Gesundheitsbereich (z. B. Covid-19)
- Politische Ereignisse und wirtschaftliche Probleme (z. B. der Krieg in der Ukraine, die Inflation)
- Feiertage und spezielle Angebotszeiträume im Jahr
Reale Beispiele für Phishing-Angriffe
Nachdem wir uns mit der Theorie befasst haben, lassen Sie uns jetzt einen Blick auf einige Praxisbeispiele für Phishing-Angriffe werfen.
Google und Facebook (2013–2015)
Einer der berüchtigtsten Phishing-Angriffe richtete sich gegen die Big-Tech-Giganten Google und Facebook.
Ein litauischer Hacker, Evaldas Rimasauskas, gab sich als Hardwarehersteller aus und brachte die Unternehmen durch seine Täuschung dazu, über 100 Millionen Dollar auf betrügerische Konten zu überweisen.
Durch die Erstellung gefälschter E-Mail-Adressen und Rechnungen, die denen eines seriösen Anbieters ähnelten, gelang es ihm, die Finanzabteilungen der Unternehmen zu täuschen.
Dieser Fall verdeutlicht nicht nur die Effektivität von BEC-Betrügereien (kurz für Business Email Compromise), einer Betrugsmethode, bei der Kriminelle gefälschte Geschäfts-E-Mails versenden, um an sensible Daten zu gelangen oder finanzielle Transaktionen auszulösen. Er zeigte auch die Wichtigkeit rigoroser Verifizierungsprozesse für finanzielle Transaktionen auf.
Wenn Sie mehr über diese Angelegenheit erfahren möchten, lesen Sie die Pressemitteilung des US-Justizministeriums.
Datenpanne bei Target (2013)
Ein Phishing-Angriff auf einen Drittanbieter führte zu einer der größten Einzelhandels-Sicherheitsverletzungen in der Geschichte.
Die Angreifenden stahlen die Zugangsdaten des Anbieters, was ihnen ermöglichte, sich Zugriff auf das Netzwerk von Target zu verschaffen und Malware auf den Kassensystemen zu installieren.
Zunächst wurde eine Phishing-E-Mail an die Mitarbeiter*innen des Anbieters geschickt, und einer von ihnen tappte in die Falle. Bei der Analyse, die nach dem Angriff durchgeführt wurde, stellte sich heraus, dass eine Zwei-Faktor-Authentifizierung (2FA) den Einbruch hätte abschwächen oder sogar verhindern können.
Durch den Einbruch wurden die Kredit- und Debitkartendaten von mehr als 40 Millionen Kund*innen kompromittiert, was zu einem erheblichen finanziellen Schaden und einer Schädigung des Unternehmensrufs führte. Dieser Vorfall zeigte die Risiken, die von Schwachstellen in der Lieferkette ausgehen.
„Phishing ist der Haupteinstiegspunkt für Ransomware und Datenschutzverletzungen. Eine einzige kompromittierte E-Mail kann ein Unternehmen Millionen kosten, nicht nur in Form von direkten finanziellen Verlusten, sondern auch in Form von Bußgeldern, Anwaltskosten und Rufschädigung.“
– Brian Krebs, Enthüllungsjournalist und Experte für Cyberkriminalität, der die Geschichte aufdeckte
Target zahlte schließlich 18,5 Millionen USD, um den Fall beizulegen.
Die vollständige Analyse des Vorfalls können Sie in der Analyse des US-Handelsministeriums nachlesen.
Die Auswirkungen von Phishing-Angriffen
Phishing-Angriffe haben weitreichende Folgen, die über das unmittelbare Opfer hinausgehen. Sie können zu erheblichen finanziellen Verlusten, Rufschädigung, behördlichen Strafen und sogar zu nationalen Sicherheitsrisiken führen.
Finanzieller Verlust
Nach Angaben des Internet Crime Complaint Center (IC3) des FBI haben Phishing-Angriffe allein im Jahr 2022 zu einem gemeldeten Schaden von über 2,7 Milliarden Dollar geführt. Unternehmen haben oft mit direkten finanziellen Verlusten zu kämpfen, die aufgrund von betrügerischen Überweisungen, nicht autorisierten Transaktionen und den Kosten, die mit der Reaktion auf den Vorfall und der Wiederherstellung verbunden sind, entstehen.
Datenschutzverletzungen und Identitätsdiebstahl
Phishing ist ein gängiger Vektor für Datenschutzverletzungen, wie die von Target, die wir gerade angesprochen haben. Wenn sich Cyberkriminelle Zugang zu Anmeldeinformationen verschaffen, können sie sensible Daten von Kund*innen und Mitarbeiter*innen nach außen schleusen.
Ein weiteres Beispiel war der Einbruch bei Equifax im Jahr 2017, bei dem die persönlichen Daten von 147 Millionen Personen offengelegt wurden. Mehr über den Fall können Sie im Bericht der Federal Trade Commission nachlesen.
Rufschaden
Organisationen, die Opfer von Phishing-Angriffen werden, erleiden eine Rufschädigung, die zu einem Verlust des Kund*innen-Vertrauens und des Marktwerts führt.
So beeinträchtigte beispielsweise Yahoos Enthüllung von mehreren Datenschutzverletzungen zwischen 2013 und 2016 den Übernahmevertrag mit Verizon, wodurch die Bewertung des Unternehmens laut Reuters um 350 Millionen Dollar sank.
So schützen Sie sich vor Phishing-Angriffen
- Seien Sie misstrauisch bei E-Mails, in denen Sie um vertrauliche Informationen gebeten werden – insbesondere, wenn es sich dabei um finanzielle Informationen handelt. Seriöse Organisationen werden niemals solche Informationen per E-Mail, Telefon oder auf anderem Wege anfordern. Achten Sie stattdessen immer auf die E-Mail-Adresse des*der Absender*in. Sie könnte sich an die eines seriösen Unternehmens anlehnen und nur einige Zeichen geändert oder weggelassen haben.
- Öffnen Sie niemals einen verdächtigen Anhang, da dies ein Standard-Übertragungsweg für Malware ist. Phisher*innen wenden gerne Einschüchterungstaktiken an und drohen möglicherweise damit, ein Konto zu deaktivieren oder Dienstleistungen zu verzögern, bis Sie bestimmte Informationen aktualisieren. Wenden Sie sich direkt an den*die Anbieter*in, um die Echtheit der Anfrage zu bestätigen.
- Achten Sie auf allgemein aussehende Informationsanfragen. Betrügerische E-Mails sind oft nicht personalisiert, während authentische E-Mails von Ihrer Bank oft auf ein Konto verweisen, das Sie bei der Bank haben. Viele Phishing-E-Mails beginnen mit „Sehr geehrter Herr/Frau“ oder anderen allgemeinen Begrüßungen/Unterschriftsformeln, und einige kommen von einer Bank, bei der Sie nicht einmal ein Konto haben.
- Lassen Sie sich nicht dazu drängen, sensible Informationen zu nennen, und übermitteln Sie diese niemals über in E-Mails eingebettete Formulare – eine sehr verbreitete Phishing-Praxis, die täglich in Ihren Junk-/Spam-Ordnern landet.
- Klicken Sie niemals auf Links in einer E-Mail, um eine Website zu öffnen, da es sich um gefälschte Hyperlinks handeln könnte. Bewegen Sie Ihren Mauszeiger über den Link und achten Sie auf den eingeblendeten Text. Stimmt dieser nicht mit dem Link überein, sollte das sofort eine Alarmglocke bei Ihnen läuten lassen. Das gilt auch für die Verwendung von URL-Verkürzungsdiensten. Öffnen Sie stattdessen ein neues Browserfenster und tippen Sie die URL direkt in die Adressleiste ein. Sie können auch überprüfen, wohin der gekürzte Link führt – dafür finden Sie weiter unten bei den Tipps zum Schutz vor Phishing einige Links. Oft sieht eine Phishing-Website identisch aus wie das Original. https://wwwpaypal.com zum Beispiel ist etwas anderes als https://www.paypal.com. Ebenso unterscheidet sich https://www.paypaI.com (mit einem großen „i“ anstelle eines kleinen „L“) vom Original https://www.paypal.com. Achten Sie unbedingt auf die Adressleiste, um sicherzustellen, dass Sie auf der richtigen Seite sind (und dass die Verbindung sicher ist und mit https:// beginnt).
„Das schwächste Glied in der Cybersicherheit ist nicht die Technologie – es ist das menschliche Element. Organisationen, die in Schulungen für das Bewusstsein rund um Phishing investieren, verringern ihr Risiko einer Gefährdung erheblich.“
– Theresa Payton, ehemalige CIO des Weißen Hauses und Beraterin für Cybersicherheit
Weitere Tipps zum Schutz vor Phishing
- Stellen Sie sicher, dass Sie eine angemessene Umgebung zur Bekämpfung von Phishing aufrechterhalten. Verwenden Sie Antivirenprogramme und zuverlässige Browser. Halten Sie Ihre gesamte Software auf dem neuesten Stand. Nutzen Sie für Ihre Kommunikation verschlüsselte Dienste wie Mailfence, um Ihre Privatsphäre weiter zu schützen.
- Verwenden Sie Passwort-Manager, die Passwörter automatisch ausfüllen, um den Überblick zu behalten, zu welchen Websites diese Passwörter gehören. Wenn der Passwort-Manager sich weigert, ein Passwort automatisch auszufüllen, sollten Sie innehalten und die Website, auf der Sie sich befinden, noch einmal überprüfen. Lesen Sie diesen Blogbeitrag, um schlechte Gewohnheiten rund um Ihre Passwörter zu vermeiden.
- Seien Sie immer misstrauisch. Phishing-E-Mails versuchen, Sie mit Warnungen in Angst und Schrecken zu versetzen, und bieten Ihnen dann eine einfache Lösung an, wenn Sie einfach nur „hier klicken!“ Oder „Sie haben einen Preis gewonnen! Klicken Sie hier, um ihn zu beanspruchen!“ Wenn Sie Zweifel haben, sollten Sie nicht klicken. Öffnen Sie stattdessen Ihren Browser, gehen Sie auf die Website des Unternehmens und melden Sie sich wie gewohnt an, um zu sehen, ob es Anzeichen seltsamer Aktivitäten gibt. Wenn Sie besorgt sind, ändern Sie Ihr Passwort.
- Nutzen Sie immer 2FA (Zwei-Faktor-Authentifizierung) wenn ein Dienst dies anbietet.
- Sie können einen bestimmten Link prüfen, bevor Sie ihn öffnen, und herausfinden, wohin er führt: Where Goes, Redirect Detective, Internet Officer Redirect Check, Redirect Check, URL2PNG, Browser Shots, Shrink The Web, Browserling.
- Zu guter Letzt sollten Sie sich über neue Trends im Phishing informieren. Sie können damit beginnen, indem Sie unseren Kurs rund um E-Mail-Sicherheit und Datenschutz machen. Er ist informativ und dabei einfach und für alle zugänglich.
Was Sie tun können, wenn Sie Phishing zum Opfer fallen
Wenn Sie auf einen Phishing-Angriff hereingefallen sind, lesen Sie unseren Blogbeitrag über gehackte E-Mails.
Sie können die Phishing-Versuche auch hier melden:
- Google: Phishing oder Badware
- US-Cert.gov: Phishing
- Consumer.ftc.gov: Phishing
Schützen Sie Ihren Computer in Zukunft zu jeder Zeit, indem Sie diese zehn Tipps anwenden.
Phishing-Trends 2025: Der Aufstieg der KI
Künstliche Intelligenz (KI) hat seit der Einführung von ChatGPT im Jahr 2022 viele Branchen auf den Kopf gestellt. Leider hat uns die Geschichte schon oft gezeigt, dass Kriminelle zu den Ersten gehören, die neue Technologien übernehmen.
Bei KI ist das nicht anders. Im Jahr 2025 erwarten wir dank des Aufstiegs der generativen KI eine Welle hochentwickelter Phishing-Angriffe. Hier sind einige Trends, auf die Sie achten sollten.
1: KI-gestützte Hyper-Personalisierung bei Phishing-Angriffen
Im Gegensatz zu herkömmlichen Massen-Phishing-E-Mails („Hallo, ich habe eine Spende für Sie …“) nutzen diese Angriffe Echtzeit-Verhaltensdaten, Social-Media-Aktivitäten und durchgesickerte Daten aus Datenschutzverletzungen, um maßgeschneiderte Nachrichten zu erstellen, die für die Empfänger*innen unglaublich authentisch wirken.
So können Angreifende beispielsweise mithilfe von KI das LinkedIn-Profil einer Zielperson, die neuesten Beiträge in den sozialen Medien oder sogar gehackte E-Mail-Muster scannen, um kontextabhängige Phishing-E-Mails zu erstellen.
Diese Nachrichten können sich auf kürzlich stattgefundene Meetings, Bewerbungen oder gar persönliche Interessen beziehen, was sie sehr überzeugend macht. KI-Chatbots können dann automatisierte Phishing-Gespräche führen und die Opfer dazu verleiten, im Verlauf des Chats – anstatt in einer einzigen E-Mail – sensible Informationen preiszugeben. Diese Taktik lässt Phishing-Versuche legitimer erscheinen und steigert ihre Erfolgsquote.
Ein Beispiel dafür im Jahr 2025 ist der Anstieg von Recruitment-Betrugsmaschen, bei denen KI-gesteuerte Bots Jobvermittler*innen imitieren und auf echte Stellenangebote bei bekannten Unternehmen verweisen, um Arbeitssuchende dazu zu bringen, persönliche Informationen und Anmeldedaten zu übermitteln.
2: Voice Phishing (Vishing) mit KI-Stimmenklonen
Das Wiederaufleben von Voice-Phishing („Vishing“) wurde durch Fortschritte in der KI-Technologie zum Klonen von Stimmen verstärkt.
Angreifende können jetzt realistische Stimmnachbildungen von Führungskräften, Kolleg*innen oder anderen vertrauenswürdigen Personen erstellen.
Mithilfe dieser geklonten Stimmen hinterlassen Cyberkriminelle überzeugende Sprachnachrichten oder führen Live-Anrufe durch, in denen sie Mitarbeitende zur Durchführung von Aktionen wie Geldüberweisungen oder die Preisgabe vertraulicher Informationen auffordern. Diese Methode nutzt das inhärente Vertrauen in vertraute Stimmen aus, was sie zu einem wirksamen Instrument der Täuschung macht.

Quelle: elevenlabs.io
Außerdem ist erwähnenswert, dass Angreifende nur zwei Minuten Ihrer Stimme benötigen, um sie überzeugend zu replizieren. Es genügen also schon ein paar Videos von Ihnen auf Instagram, um Ihre Stimme (oder die von nahen Verwandten) zu kopieren!
3: Phishing-as-a-Service (PhaaS)
Das Ökosystem der Cyberkriminalität hat den Aufstieg von Phishing-as-a-Service-Plattformen erlebt.
Diese Dienste bieten fertige Phishing-Kits mit Vorlagen, Hosting und sogar Kundensupport an und senken damit die Einstiegshürde für angehende Cyberkriminelle.
Einige PhaaS-Angebote enthalten KI, um Phishing-Kampagnen zu automatisieren und zu optimieren und so ihre Reichweite und Wirksamkeit zu erhöhen. Diese Kommerzialisierung von Phishing-Tools hat zu einem Anstieg der Anzahl und Vielfalt von Phishing-Angriffen geführt, da selbst Personen mit minimalen technischen Kenntnissen raffinierte Kampagnen starten können.
Fazit
Cyberkriminelle, die oft von Regierungen oder sehr mächtigen Mafias unterstützt werden, bewegen sich äußerst schnell, und ihre Kreativität kennt keine Grenzen. Sie finden ständig neue Taktiken und neue Schwachstellen, die sie ausnutzen können.
Andererseits neigen wir (Nutzer*innen) dazu, die Anzahl der Geräte zu vervielfachen, mit denen wir online gehen … was neue Türen für mögliche Angriffe öffnet. Daher ist es wichtig, in Sachen Cybersicherheit informiert zu bleiben.
Vor allem aber sollten Sie sich auf Ihren gesunden Menschenverstand verlassen. Sie können kein Gewinnspiel gewinnen, an dem Sie nicht teilgenommen haben. Ihre Bank wird Sie nicht über eine E-Mail-Adresse kontaktieren, die Sie dort nie angegeben haben. Kennen Sie die Warnzeichen, denken Sie nach, bevor Sie klicken, und geben Sie niemals Ihr Passwort oder Ihre Finanzdaten weiter.
Übrigens ist es unerlässlich, eine verschlüsselte E-Mail-Suite wie Mailfence zu haben, um Ihre Kommunikation zu schützen und alle Arten von Betrug zu vermeiden.
Genau genommen wurde Mailfence entwickelt, um Sie vor Cyber-Bedrohungen und Verletzungen Ihrer Privatsphäre zu schützen, einschließlich Phishing. Zusätzlich zur Ende-zu-Ende-Verschlüsselung von E-Mails bieten wir digitale Signaturen und 2FA. Und falls Sie es noch nicht wussten: Mailfence ist nicht nur eine E-Mail-Lösung, sondern auch ein kollaboratives Office-Paket.
Registrieren Sie sich noch heute für ein kostenloses Mailfence-Konto und machen Sie den ersten Schritt zum Schutz Ihrer Kommunikation.



