Ransomware-Angriffe können Sie innerhalb von Sekunden aus Ihrem eigenen Computer aussperren. Und was noch schlimmer ist: Selbst wenn Sie das Lösegeld bezahlen, gibt es keine Garantie, dass Sie den Zugriff auf Ihre Daten oder Ihr Geld zurückbekommen.
Und dank KI verfeinern Cyberkriminelle ihre Angriffe – und niemand ist dagegen immun.
Ganz egal, ob Sie eine Privatperson oder ein Unternehmen sind, wir zeigen Ihnen alles, was Sie über Ransomware-Angriffe wissen müssen, unter anderem zu diesen Themen:
- Wie sehen Ransomware-Angriffe aus?
- Wie erkenne ich einen Ransomware-Angriff?
- 8 Schritte, die Sie heute befolgen können, um Ihre Dateien vor Hacker*innen zu schützen.
Lassen Sie uns direkt loslegen.
Mailfence – Ihre sichere Produktivitätssuite
Holen Sie sich Ihre Privatsphäre zurück mit
- Nachrichten
- Kalendern
- Dokumenten
- Gruppen
Was ist ein Ransomware-Angriff?
Ransomware ist ein Schmelzwort aus den beiden Wörtern „Lösegeld“ (im Englischen ransom) und „Software“. Im Wesentlichen handelt es sich dabei um eine Software, die Ihren Computer „sperrt“, bis Sie ein Lösegeld zahlen.
Genauer gesagt „verschlüsselt“ ein Ransomware-Angriff Ihre Inhalte (Dokumente, Videos, Fotos, in Apps gespeicherte Daten etc.). Haben Sie ein Finanzdokument, das Sie bearbeiten müssen? Sie haben keinen Zugriff mehr darauf. Haben Sie ein Video von Ihren Kindern im Urlaub? Sie können es sich nicht mehr anschauen.
Die Hacker*innen kontaktieren Sie und fordern ein Lösegeld. Im Gegenzug versprechen sie, Ihnen den Schlüssel zur Entschlüsselung Ihrer Daten zu geben, sodass Sie wieder Zugriff auf all Ihre Dateien erhalten. Doch hier gibt es mehrere Probleme:
- Erstens: Das Lösegeld ist nicht billig. Laut dem State of Ransomware 2024 Report von Sophos wurde die durchschnittliche Ransomware-Zahlung auf zwei Millionen US-Dollar geschätzt.
- In den letzten Jahren haben die Angreifer*innen jedoch begonnen, ihre Lösegeldforderungen an ihre Opfer anzupassen. Es kann zum Beispiel sein, dass sie „nur“ ein paar tausend Dollar Lösegeld verlangen, um die Wahrscheinlichkeit zu erhöhen, dass Sie zahlen.
- Und schließlich: Wer garantiert Ihnen, dass die Hacker*innen Ihnen tatsächlich wieder Zugang zu Ihren Daten gewähren werden? Warum sollten Sie nicht noch mehr Geld verlangen?
Das macht Ransomware-Angriffe zu einer extrem belastenden Angelegenheit. Wenn Sie einer solchen Attacke zum Opfer gefallen sind, gibt es möglicherweise nicht immer eine Möglichkeit, Ihre Daten wiederherzustellen (dazu später mehr).
Ransomware gelangt, genau wie andere Arten von Viren, oft über Phishing-E-Mails auf Ihren Computer. Die Angreifer*innen können auch verschiedene Social-Engineering-Techniken anwenden, um ihre Opfer zur Installation der schädlichen Software zu verleiten.
Es gibt zwei Arten von Ransomware-Angriffen:
- Verschlüsselnde Ransomware: bezieht fortschrittliche Verschlüsselungsalgorithmen mit ein, die Dateien unlesbar machen sollen. Die Opfer werden zu einer Zahlung aufgefordert, um den Schlüssel zu erhalten, mit dem die blockierten Inhalte entschlüsselt werden können.
- Locker-Ransomware: Diese Art Ransomware sperrt das Opfer aus dem Betriebssystem aus und macht es unmöglich, auf den Desktop und Anwendungen oder Dateien zuzugreifen. Die Opfer müssen zahlen, um ihre Daten wieder zu entsperren.
3 Beispiele für Ransomware-Angriffe aus dem wahren Leben
Es ist wichtig, dass Sie verstehen, dass Ransomware-Angriffe sowohl auf Unternehmen als auch auf Privatpersonen erfolgen können. In den folgenden Beispielen werfen wir einen Blick auf einige bekannte Fälle solcher Angriffe, wie sie abgelaufen sind und welche Schwachstellen sie ausgenutzt haben.
Der Angriff auf Colonial Pipeline
Im Mai 2021 machte der Ransomware-Angriff auf Colonial Pipeline in den gesamten USA Schlagzeilen.
Colonial Pipeline – einer der größten Kraftstofflieferanten in den USA – wurde Opfer der Ransomware DarkSide, einer ausgeklügelten Malware, die von einer Gruppe mutmaßlich russischer Cyberkrimineller entwickelt wurde.
Dank eines einzigen kompromittierten Passworts, das im Dark Web aufgetaucht war, erhielten die Angreifenden Zugang zum IT-Netzwerk von Colonial Pipeline. Zu den Schwachstellen, die den Angriff ermöglichten, gehörten außerdem:
- Fehlende Multi-Faktor-Authentifizierung (MFA oder 2FA): Das angegriffene Konto war nur durch ein Passwort geschützt, sodass es für die Angreifer*innen ein Leichtes war, sich Zugang zu verschaffen.
- Flache Netzwerkarchitektur: Die IT-Systeme waren miteinander verbunden, sodass die Ransomware-Attacke tiefer in die kritische Infrastruktur eindringen konnte.
- Verzögerte Reaktion auf den Vorfall: Das Unternehmen entdeckte die Sicherheitslücke am 7. Mai 2021, reagierte aber nicht rechtzeitig, sodass sich die Malware verbreiten und wichtige Daten verschlüsseln konnte.
machte in den USA Schlagzeilen.
Dieser Ransomware-Angriff hatte schwerwiegende Folgen für die amerikanische Öffentlichkeit, denn er zwang das gesamte Kraftstoffverteilungsnetz zum Stillstand und verursachte einen Benzinmangel an der gesamten Ostküste der USA.
In Zusammenarbeit mit dem FBI zahlte Colonial Pipeline schließlich 4,4 Millionen USD in Bitcoin. Ungefähr die Hälfte des Wertes der Bitcoins wurde später wieder eingezogen.
Details zu diesem Ransomware-Angriff erfahren Sie auf der Website des US-Justizministeriums.
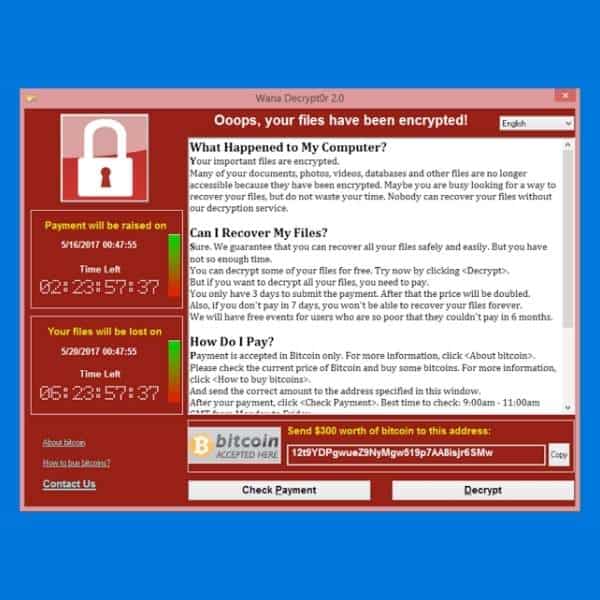
Die WannaCry-Ransomware-Epidemie
Der Ausbruch der Ransomware WannaCry im Mai 2017 (auch bekannt als WannaCrypt) war einer der am weitesten verbreiteten Cyberangriffe in der Geschichte. Innerhalb eines einzigen Tages wurden über 300.000 Computer in mehr als 150 Ländern infiziert.
Der Angriff basierte auf einer Windows-Schwachstelle namens EternalBlue, die von der Nationalen Sicherheitsbehörde der USA (NSA) gestohlen und von einer Hackergruppe namens The Shadow Brokers veröffentlicht worden war.
WannaCry ist ein sogenannter „Ransomware-Kryptowurm“:
- Nachdem er einen Computer infiziert hat, fordert er ein Lösegeld, das in Bitcoin („Krypto“) zu zahlen ist.
- Außerdem konnte er sich selbstständig ausbreiten („Wurm“).
Einige der Schwachstellen, die bei diesem Angriff ausgenutzt wurden, waren:
- Ungepatchte Windows-Systeme: WannaCry zielte auf Computer ab, auf denen veraltete Windows-Versionen (Windows 7, XP, Server 2003) liefen, für die es keine wichtigen Sicherheitsupdates gab.
- Selbstreplizierende Malware: Im Gegensatz zu typischen Ransomware-Angriffen verbreitete sich WannaCry selbstständig und konnte so ohne irgendeine Interaktion der Nutzer*innen ganze Netzwerke infizieren.
- Langsame Reaktion der Unternehmen: Microsoft hatte zwei Monate vor dem Angriff einen Sicherheits-Patch (MS17-010) veröffentlicht, aber viele Unternehmen versäumten es, ihre Systeme rechtzeitig zu aktualisieren.
Im Vereinigten Königreich hat der Ransomware-Angriff WannaCry den Nationalen Gesundheitsdienst (NHS) zum Stillstand gebracht und Dutzende Krankenhäuser lahmgelegt.
Auch viele multinationale Unternehmen wie FedEx und Nissan waren gezwungen, ihren Betrieb einzustellen. Der Angriff wurde später der nordkoreanischen Lazarus-Gruppe zugeschrieben, die die Lösegeldzahlungen zur Finanzierung weiterer Aktionen im Cyber-Krieg verwendete.
Weitere Informationen zu diesem Angriff finden Sie im Blogartikel von Microsoft.
Der Kaseya-VSA-Angriff
Im Juli 2021 wurde mithilfe einer von der REvil-Gruppe entwickelten Ransomware eine Zero-Day-Schwachstelle in Kaseya VSA ausgenutzt. Kaseya VSA ist eine Software zur Fernverwaltung von IT-Systemen, die von Tausenden Unternehmen weltweit eingesetzt wird.
Durch das Hacken des zentralen Softwareverteilungssystems von Kaseya war REvil in der Lage, Ransomware-Updates an die Kund*innen von Kaseya zu verteilen und so auf einen Schlag über 1.500 Unternehmen zu infizieren.
Der Ransomware-Angriff basierte auf mehreren wichtigen Sicherheitslücken:
- Die Angreifer*innen entdeckten eine ungepatchte Schwachstelle in der Software von Kaseya und nutzten sie aus, bevor das Unternehmen sie beheben konnte.
- Angriff auf die Lieferkette: Kaseya VSA war ein vertrauenswürdiges Remote-Management-Tool und hatte daher direkten Zugang zu den Client-Systemen. Das erleichterte das Verteilen von Malware, ohne dass Sicherheitswarnungen ausgelöst wurden.
- Keine Segmentierung in IT-Netzwerken: Viele betroffene Unternehmen hatten keine Trennung zwischen IT-Management-Tools und kritischen Systemen, sodass sich der Angriff schnell über die Netzwerke ausbreiten konnte.
Was diese Attacke von den anderen, über die wir berichtet haben, unterscheidet, ist die Art und Weise, wie Ransomware-as-a-Service (RaaS) zur Ausweitung der Cyberkriminalität eingesetzt wird.
Bei einem RaaS-Modell erstellen die Ransomware-Entwickler*innen die Malware, verlassen sich aber zur Verteilung auf Partner*innen.
In diesem Fall arbeitet REvil im Grunde wie ein kriminelles SaaS-Unternehmen, das den Zugang zu seinen Ransomware-Tools gegen einen Prozentsatz der Lösegeldzahlungen verkauft. Die Partner*innen von REvil waren dafür verantwortlich, die Systeme von Kaseya anzugreifen und zu infiltrieren. Im Gegenzug behielten die Partner*innen einen Teil (oft 60–80 Prozent) des gezahlten Lösegelds, während REvil den Rest einkassierte.
Insgesamt waren mehr als 1.500 Unternehmen weltweit infiziert, darunter Supermärkte, IT-Firmen und Finanzinstitute.
Die Bedeutung von KI für Ransomware-Angriffe
Das Aufkommen von ChatGPT und die massenhafte Verbreitung von generativer KI im Jahr 2022 hat viele Branchen revolutioniert. Cyberkriminelle sind von diesem Trend nicht ausgenommen und machen sich den Einsatz von KI massiv zunutze, um ihre Angriffe zu verfeinern.
Im Folgenden lesen Sie fünf Möglichkeiten, wie KI Angreifenden hilft, ihre Ransomware-Angriffe ausgeklügelter und raffinierter zu gestalten.
Hochgradig personalisierte Phishing-E-Mails
Wie bereits erläutert, sind Phishing-E-Mails nach wie vor einer der wichtigsten Angriffsvektoren für Ransomware-Attacken.
KI kann jetzt Social Media, E-Mails und geleakte Datenbanken effektiv auswerten, um maßgeschneiderte Phishing-Nachrichten zu erstellen, die sehr überzeugend wirken. Anstelle von allgemeinem Spam erhalten die Opfer E-Mails, die echte Gespräche, Rechnungen oder dringende Sicherheitswarnungen imitieren.
Polymorphe Ransomware
Traditionelle Ransomware ist leichter zu erkennen, weil sie bekannten Mustern folgt. KI-gesteuerte polymorphe Ransomware mutiert ständig ihren Code, sodass sie für signaturbasierte Antivirenprogramme unsichtbar ist. Jede Infektion unterscheidet sich geringfügig, was es nahezu unmöglich macht, sie auf eine schwarze Liste zu setzen.
Automatisierte Ziel-Auswahl und Verbreitung
KI scannt riesige Datensätze in Echtzeit, identifiziert anfällige Unternehmen mit schwachen Cybersicherheitsmaßnahmen und priorisiert hochwertige Ziele. Cyberkriminelle können dann Angriffe auf mehrere Unternehmen gleichzeitig starten und mit minimalem Aufwand ihren Profit maximieren.
Weiterhin können KI-gesteuerte Bots automatisch in Unternehmensnetzwerke eindringen, nach Schwachstellen suchen und Ransomware ohne menschliches Zutun verbreiten.
Der Einsatz von KI-gestützten Hacking-Tools hat zu einer Zunahme von vollautomatischen Ransomware-Angriffen geführt, die weniger menschliches Fachwissen zur Ausführung erfordern.
KI-gestütztes Ausweichen
Moderne Cybersicherheits-Tools stützen sich auf maschinelles Lernen, um Ransomware-Muster zu erkennen – aber Angreifer*innen setzen KI gegen KI ein, um die Erkennung zu umgehen.
Cyberkriminelle können beispielsweise ihre Ransomware gegen KI-gestützte Sicherheitstools trainieren und verschiedene Angriffsmethoden testen, bis sie die Erkennung umgehen.
Einige KI-gesteuerte Ransomware täuscht die Verschlüsselung zunächst vor, indem sie Sicherheitstools vorgaukelt, der Angriff sei gestoppt, während sie die Verschlüsselung von Dateien im Stealth-Modus fortsetzt.
Lösegeldverhandlung
Die KI verändert sogar die Art und Weise, wie Cyberkriminelle Lösegelder aushandeln, und macht sie effektiver und psychologisch manipulativ.
Anstatt dass menschliche Hacker*innen die Verhandlungen führen, werden jetzt Bots eingesetzt, um mit den Opfern zu kommunizieren.
Diese Bots analysieren die Reaktionen der Opfer, passen die Lösegeldforderungen an und setzen Unternehmen unter Druck, schneller zu zahlen.
KI wird auch eingesetzt, um Finanzunterlagen, Versicherungspolicen und öffentliche Gewinnberichte zu scannen, um das höchste Lösegeld zu berechnen, das sich ein Unternehmen wahrscheinlich leisten kann.
Was können Sie tun, wenn Sie Opfer eines Ransomware-Angriffs geworden sind?
Sind Sie einem Ransomware-Angriff zum Opfer gefallen? Dann sollten Sie sofort diese drei Schritte befolgen:
- Stoppen Sie die Ausbreitung. Der erste Schritt besteht darin, den Angriff zu stoppen. Ransomware kann schnell ganze Netzwerke infizieren, daher zählt jede Sekunde. Trennen Sie Ihr Gerät sofort von WLAN, Ethernet und externen Speichermedien (USB-Sticks, Backup-Laufwerke). Wenn Sie sich in einem Unternehmensnetzwerk befinden, alarmieren Sie sofort die IT-Sicherheitsabteilung, damit sie die Bedrohung eindämmen kann, bevor diese das gesamte System lahmlegt.
- Kennen Sie Ihren Feind. Nicht alle Ransomware-Angriffe sind gleich. Einige verfügen über bekannte Entschlüsselungstools, während andere Ihre Dateien dauerhaft löschen können, selbst wenn Sie bezahlen. Machen Sie einen Screenshot der Lösegeldforderung – dieser enthält oft Hinweise auf den Angriff. Verwenden Sie dann Online-Tools wie ID Ransomware, um die Ransomware-Variante zu identifizieren. Sie können auch beim No More Ransom Project nachsehen, ob es ein kostenloses Entschlüsselungstool gibt.
- Melden Sie den Angriff. Bevor Sie ein Lösegeld zahlen, sollten Sie Profis für Cybersicherheit und die Strafverfolgungsbehörden einschalten. Die Zahlung ist keine Garantie für die Wiederherstellung der Dateien. Melden Sie den Angriff dem Internet Crime Complaint Center (IC3) des FBI sowie der Cybersicherheitsbehörde Ihres Landes (CISA in den USA, Europol etc.). Und schließlich sollten Sie Ihr IT-Team oder Ihren Cybersicherheitsanbieter einschalten.
Beachten Sie jedoch, dass nicht jede Ransomware wieder entschlüsselt werden kann. Bei vielen Ransomware-Angriffen sind die Daten leider verloren. Deshalb ist Vorbeugung nach wie vor Ihr bester Schutz gegen zukünftige Angriffe.
8 Tipps, wie Sie Ransomware-Angriffe umschiffen
Inzwischen haben Sie sicher verstanden, dass Ransomware-Angriffe eine sehr reale Bedrohung darstellen. Lassen Sie uns also acht einfach zu befolgende Tipps durchgehen, mit denen Sie solche Angriffe verhindern können.
1: Erstellen Sie regelmäßige Backups
Backups sind bei weitem der beste Weg, um sich vor Ransomware-Angriffen zu schützen … Solange Sie sie effizient durchführen.
Es ist wichtig, dass Sie für jedes Backup mehrere Kopien Ihrer Dateien erstellen und diese auf verschiedenen Medien aufbewahren. Idealerweise sollten Sie jede Kopie separat und an verschiedenen Orten aufbewahren. Im optimalen Fall bewahren Sie eine Kopie offline (auf einem sicheren externen Datenträger) auf, eine weitere Kopie könnten Sie in einem sicheren und privaten Cloud-Dienst speichern.
Vermeiden Sie es außerdem, das Backup-Medium (zum Beispiel eine externe Festplatte) nach einem Backup an das Computersystem angeschlossen zu lassen. Im Falle einer Infektion Ihres Systems besteht die Gefahr, dass auch das externe Laufwerk infiziert wird, was Ihr Backup unbrauchbar machen würde.
Lesen Sie unsere Tipps für sichere Backups Ihrer Daten, damit Sie effiziente Datensicherungen erstellen können!
2: Nutzen Sie aktuelle Software
Software-Updates enthalten oft „Sicherheits-Patches“, die Schwachstellen beheben sollen, welche Hacker*innen ausnutzen könnten, um Cyberangriffe (einschließlich Ransomware-Angriffe) zu starten.
Deswegen ist es wichtig, dass Sie Updates für diese Software, Geräte und Peripheriegeräte sofort herunterladen, sobald Sie eine Benachrichtigung über deren Existenz erhalten. Denn wenn Sie diese Benachrichtigung erhalten haben, sind Sie damit nicht allein… Jetzt wissen die Hacker*innen, dass das betreffende Gerät oder die Software eine Schwachstelle aufweist.
Eine weitere gute Idee ist es, die auf Ihrem Computer oder System installierten Programme auf das absolute Minimum zu beschränken. Deinstallieren Sie ungenutzte Software. Vergessen Sie nicht, auch veraltete Plug-ins aus Ihrem Browser zu entfernen. Das gilt auch für Ihr Smartphone: Deinstallieren Sie alle Apps, die Sie nicht mehr nutzen.
3: Wenden Sie das Prinzip des geringsten Privilegs (PoLP) an
Um Ransomware-Angriffe zu verhindern, können Sie auch das PoLP (Principle of Least Privilege) befolgen. Das bedeutet, dass Sie die Nutzung Ihres Geräts/Computersystems auf zwei getrennte Konten aufteilen:
- Ein Standardkonto, das Sie täglich nutzen und das nur die nötigsten Funktionen aufweist.
- Ein Admin-Konto, das Ihnen den Zugriff auf den Kern Ihres Geräts/IT-Systems gewährt (zum Beispiel um Einstellungen zu ändern oder Software zu installieren/deinstallieren). In diesem Konto haben Sie die vollen Rechte auf Ihrem System, und Sie melden sich nur dann an, wenn Sie solche Aufgaben ausführen müssen.
Im Falle eines Ransomware-Angriffs wird der Schaden auf Ihr Standardkonto begrenzt. Die Ransomware kann nicht auf Kernkomponenten Ihres Computers zugreifen, da diese Zugriffe durch das Admin-Konto kontrolliert werden.
4: Erkennen und vermeiden Sie Phishing-Versuche
Viele Ransomware-Angriffe werden durch Phishing-, Spear-Phishing- oder Whaling-E-Mails oder durch Smishing eingeleitet. Oftmals laden die Opfer einen Anhang dieser Nachrichten herunter und erlauben so der Ransomware, in ihren Computer, ihr Telefon oder ihr Computersystem einzudringen.
Deshalb sollten Sie nur Anhänge und Links öffnen, die von wirklich vertrauenswürdigen Quellen stammen. Das heißt im Klartext: Klicken Sie nicht auf einen Link in einer E-Mail. Selbst hinter einem scheinbar unschuldigen Hinweis wie „Klicken Sie hier, um sich abzumelden“ kann sich gefürchtete Ransomware verbergen. Loggen Sie sich stattdessen mit der URL, die Sie normalerweise verwenden, auf der entsprechenden Website ein.
5: Makros? Nein, danke!
Öffnen Sie niemals eine Microsoft-Office-Datei, die Makros enthält, ohne sich vorher von dem*der Absender*in der Nachricht bestätigen zu lassen, dass die Datei wirklich von ihm*ihr stammt und dass diese Makros nicht schädlich sind.
6: Installieren Sie ein seriöses Antivirenprogramm, um Ransomware-Angriffe zu erkennen
Es versteht sich von selbst, dass Sie Ihr Gerät mit einem Antivirusprogramm vor Malware schützen sollten. Leider ist der angebotene Schutz begrenzt, da ein Antivirenprogramm nur Malware erkennen kann, die schon anderswo entdeckt wurde. Aber zumindest können Sie bereits bekannte Ransomware-Angriffe vermeiden, was schon eine gute Sache ist.
7: Nutzen Sie ein VPN
Es ist nützlich, ein VPN zu verwenden, wenn Sie in öffentlichen WLANs surfen. Diese Netzwerke bieten nämlich keinen Schutz vor Hacking und sind aus diesem Grund bei Hacker*innen sehr beliebt. Die Nutzung eines VPNs verhindert ein mögliches Abfangen von Daten, die dazu verwendet werden könnten, in Ihre Geräte oder Ihr Computersystem einzudringen.
8: Verwenden Sie eine virtuelle Maschine
Virtuelle Maschinen werden hauptsächlich dazu verwendet, ein IT-System zu duplizieren, um neue Software zu testen oder zwei verschiedene Betriebssysteme auf demselben Computer auszuführen.
Sie können aber auch verwendet werden, um Angriffe durch bösartige Software zu verhindern. In dieser Hinsicht können sie Ihnen also helfen, Ransomware-Angriffe zu vermeiden. Sie sollten jedoch wissen, dass sie nicht immer wirksam sind. Leistungsstarke Ransomware kann besonders gefährlich sein.
Ransomware-Angriffe verhindern: So kann Mailfence Ihnen helfen
Damit sind wir am Ende dieses Leitfadens angelangt. Wir hoffen, dass Sie nun besser verstehen, wie Ransomware-Angriffe funktionieren und wie ein Ransomware-Schutz aussehen kann.
Sind Sie bereit, Ihre persönliche Cybersicherheit auf die nächste Stufe zu heben?
Dann sollte Ihr erster Schritt darin bestehen, einen privaten und sicheren E-Mail-Anbieter zu wählen. Im Gegensatz zu Gmail oder Yahoo stellt Mailfence Ihre Privatsphäre und Ihre Sicherheit über den Profit. Wir sind besonders stolz darauf, Ihnen diese Features zu bieten:
- Fortschrittliche Sicherheitstools: Ende-zu-Ende-Verschlüsselung, symmetrische Verschlüsselung, digitale Signaturen und vieles mehr.
- Kein Tracking, keine Werbung. Wir verwenden keine Werbe- oder Marketing-Tracker von Dritten. Außerdem verfolgen wir Ihre Aktivitäten in der Anwendung nicht. Mailfence ist vollkommen werbefrei.
- Strenge Datenschutzgesetze. Die Server von Mailfence befinden sich in Belgien, wo strenge Gesetze zum Schutz der Privatsphäre herrschen. Nur ein gültiger belgischer Gerichtsbeschluss kann uns zur Herausgabe von Daten zwingen.
Möchten Sie Ihren digitalen Fußabdruck verkleinern und Ihre Cybersicherheit auf die nächste Stufe heben? Erstellen Sie jetzt Ihr kostenloses Konto!
Mailfence – Ihre sichere Produktivitätssuite
Holen Sie sich Ihre Privatsphäre zurück mit
- Nachrichten
- Kalendern
- Dokumenten
- Gruppen