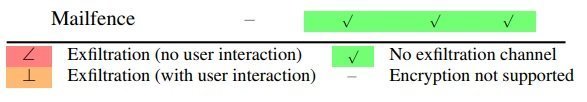
New vulnerabilities in many OpenPGP and S/MIME enabled email clients were announced yesterday. These “Efail” vulnerabilities have attracted a lot of attention in the media. As per our analysis, Mailfence is not impacted by the OpenPGP Efail vulnerability. Also, based on the mentioned issues in the technical paper, the OpenPGP protocol itself is safe to use, if you are not using it with a buggy email client.
OpenPGP vulnerabilities disclosed in the Efail vulnerability paper: why Mailfence is not impacted
There are two attacks of concern demonstrated by the security researchers. However, to pull it off:
- the attacker needs access to the encrypted emails, e.g., by compromising email accounts, email servers, backup systems or by eavesdropping on network traffic.
- the attacker needs to send or replay the intercepted/modified emails towards its destination.
1. “Direct exfiltration” attack
This type of attack takes advantage of the fact that modern e-mail programs choose to display HTML to the user. The attacker in this case, simply constructs the new email message (from the old/captured one) starting with a plaintext part having an <img> or <style> tag enclosing the captured ciphertext, and finally sending it to the recipient. When the recipient email client displays the entire decrypted message, including the captured ciphertext (as unencrypted text), the active content for externally loaded images or styles, will exfiltrate the plaintext through requested URLs to a remote server.
Why is Mailfence not impacted by the “direct exfiltration” attack?
Upon receiving encrypted emails (ASCII-armored PGP messages), or emails with nested encrypted content (a mix of plaintext and ciphertext), Mailfence never attempts to decrypt them on the fly or automatically. This is because it requires users’ private key passphrase that only the user knows.
Thus, when a user opens such a message, an attempted attack of this type would only result in the encrypted text being sent in the requested URL (which, as per the attack requirements, the attacker would have already), and this only if the user chooses to load remote content, which is always disabled by default.
For all nested ciphertexts, are only decrypted when the user explicitly clicks on the ‘Decrypt it‘ prompt (for that nested cipher text block only). However, they will only be decrypted in plain-text mode – effectively making it impossible for this kind of attack to succeed.
2. “Malleability Gadget” Attack
This second vulnerability takes advantage of OpenPGP’s lack of mandatory integrity verification that has been known to the developer community since 1999. This corresponds to the malleability aspect of Cipher Feedback Mode (CFB), the mode of encryption that OpenPGP uses for its symmetric encryption operations. As a result, in combination with specified exfiltration channels, an attacker can recover plaintext (out of the captured ciphertext) via Chosen-Ciphertext Attack as soon as the email client opens the modified message in decrypted form.
Why is Mailfence not impacted by the “malleability gadget” attack?
Mailfence uses the open-source openpgpjs library for its front-end that handles the end-to-end encryption and decryption operations. This library uses the Symmetrically Encrypted with Integrity Protection (SEIP) OpenPGP packet, which encapsulates the use of Modification Detection Code (MDC) for plaintext integrity checks. If the integrity check fails (or does not exist), the library will refuse and not load the decrypted content. If the SEIP packet is turned into Symmetrically Encrypted (SE) packet – another method that researchers highlighted – the library will not support it (as it regards this practice as obsolete).
Recommendations for OpenPGP users using affected email clients
Since Efail is not a vulnerability in OpenPGP itself, it is in fact linked to buggy email clients. We would therefore recommend you to take the following mitigation steps, if you are using your Mailfence account with any of the listed buggy email clients.
- Decrypt mail outside of email client:
Using a separate application (command-line based) outside of your email client to decrypt incoming emails will prevent the opening of exfiltration channels. This will require you to save the incoming message in a file and then opening it up using a command-line. - Disable HTML rendering and Remote Content Loading:
Preventing your email client from rendering HTML and loading remote content will prevent the predominant form of establishing exfiltration channels. Please refer to the specific documentation of your email client in this regard.
Again, as the vulnerabilities are not in the OpenPGP protocol itself, needless to say, apply updates to your OpenPGP based email client as soon as they are available.
Other points regarding Efail vulnerability
- OpenPGP remains one of the best ways for encrypting emails, and if implemented correctly and used securely, can be relied upon. The highlighted Efail vulnerability issues by the security researchers corresponds on how end-to-end encryption protocols interact with modern email programs implementing those protocols. This does mean, that if any of your recipient is using the buggy email client, then it could potentially exfiltrate the plaintext of encrypted emails. Another reason why you should encourage others to use secure and private email services like Mailfence.
- At Mailfence, by default, all end-to-end encrypted emails are always sent with digital signatures, a practice that you should advocate among your social and professional circles. Also check our OpenPGP encryption + digital signing best practices blogpost, and apply TFA on your accounts.
As one of the most secure and private email suites, we take security and privacy of user data very seriously and strive to improve our service in every possible way. Contact us in case you have suggestions or queries. Learn more about Mailfence on our press page.
Follow us on twitter/reddit and keep yourself posted at all times.
![Mailfence_not_impacted_by_Efail_vulnerabilities[1] ""](https://blog.mailfence.com/wp-content/uploads/elementor/thumbs/Mailfence_not_impacted_by_Efail_vulnerabilities1-qp61j4a3mljnyibz0oasf8pyiarsorzn696qdk68i0.png)



